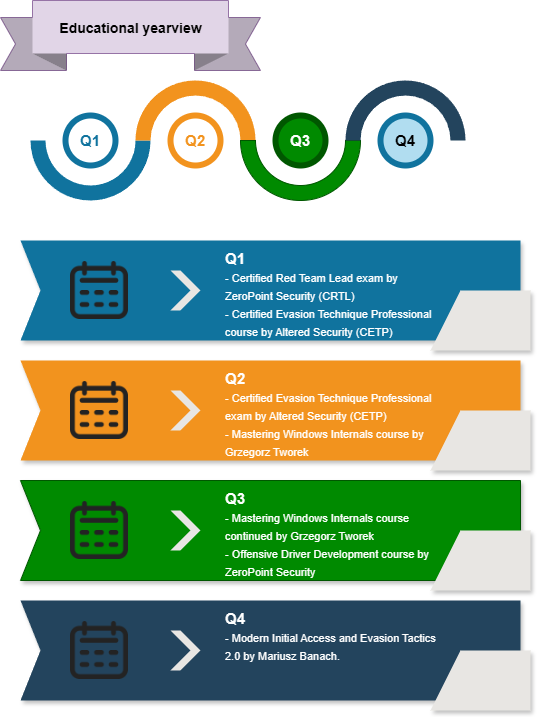
Educational yearview
I will have less time for studies and courses this year than I would like, so I will attempt to set my goals for courses and certifications already at the start of the year. I hope this will help me not get too distracted by all the shinies.
I made this foolish model to try and visualize my ambition for the year, maybe even practice my mindmapping and presentation skills while I was at it. Way to go on that however.
I will start the first quarter of the year by finishing CRTL, hopefully. I feel somewhat prepared for the task at hand in regards to bypasses the present version of Elastic EDR with what I picked up from the course. I might even do a post here or on Github with my code, if I feel confident in it.
I have purchased the Certified Evasion Technique Professional by Altered Security in pre-order. And it was promised to arrive in February, so hopefully I can start with the course sometime in February as well. The course promises tackling EDR evasion, EDR killing with BYOVD, kernel programming and more advanced topics of Windows exploitation. I see some overlap with CRTL already from the content table, but I am not too worried as I still need more practical experiecing researching these topics.
I have followed Grzegorz Tworek on Twitter for a while and I am very curious to see what this course is gonna unfold to be. There isn’t a certification along with this course, but I certainly don’t mind as this year I feel I have less to prove and will just focus on deep learning. The content table of the course does not promise a whole lot to be honest, but it mentions targeting penetration testers, so there is that. I have confidence it will be at help to furthering competence in researching Windows, as I aspire to do more.
Mastering Windows Internals by Grzegorz Tworek
I have had eyes on the first verison of this course for some time, but I haven’t been ready or had the time. So when an update was promise, I became eager to persue this course. Initial access is something that is continously interesting to me, even though maybe not always a skill I can utilize in my job. This could be a subject of change of course. I will await the release of to purchase, but I am pretty confident in this choice currently.
Modern Initial Access and Evasion Tactics
If Rasta made it, I gotta own it. So yeah, not much explaining to be had here. Probably gonna be pretty sick and tired of Kernels and drivers by the end of this year. But hey, maybe i’ll look even older…
Offensive Driver Development by ZeroPoint Security
I doubt anyone will ever make it this far, but the next blogpost will be a techical one and hopefully somewhat exciting to the Windows appreciating audience.
-> BirkeP